The login page for the criminal reshipping service SWAT USA Drop.
One of the largest cybercrime services for laundering stolen merchandise was hacked recently, exposing its internal operations, finances and organizational structure. Here’s a closer look at the Russia-based SWAT USA Drop Service, which currently employs more than 1,200 people across the United States who are knowingly or unwittingly involved in reshipping expensive consumer goods purchased with stolen credit cards.
Among the most common ways that thieves extract cash from stolen credit card accounts is through purchasing pricey consumer goods online and reselling them on the black market. Most online retailers grew wise to these scams years ago and stopped shipping to regions of the world most frequently associated with credit card fraud, including Eastern Europe, North Africa, and Russia.
But such restrictions have created a burgeoning underground market for reshipping scams, which rely on willing or unwitting residents in the United States and Europe to receive stolen goods and relay them to crooks living in the embargoed areas.
Services like SWAT are known as “Drops for stuff” on cybercrime forums. The “drops” are people who have responded to work-at-home package reshipping jobs advertised on craigslist.com and job search sites. Most reshipping scams promise employees a monthly salary and even cash bonuses. In reality, the crooks in charge almost always stop communicating with drops just before the first payday, usually about a month after the drop ships their first package.
The packages arrive with prepaid shipping labels that are paid for with stolen credit card numbers, or with hijacked online accounts at FedEx and the US Postal Service. Drops are responsible for inspecting and verifying the contents of shipments, attaching the correct shipping label to each package, and sending them off via the appropriate shipping company.
SWAT takes a percentage cut (up to 50 percent) where “stuffers” — thieves armed with stolen credit card numbers — pay a portion of each product’s retail value to SWAT as the reshipping fee. The stuffers use stolen cards to purchase high-value products from merchants and have the merchants ship the items to the drops’ address. Once the drops receive and successfully reship the stolen packages, the stuffers then sell the products on the local black market.
The SWAT drop service has been around in various names and under different ownership for almost a decade. But in early October 2023, SWAT’s current co-owner — a Russian-speaking individual who uses the handle “Fearlless” — took to his favorite cybercrime forum to lodge a formal complaint against the owner of a competing reshipping service, alleging his rival had hacked SWAT and was trying to poach his stuffers and reshippers by emailing them directly.
Milwaukee-based security firm Hold Security shared recent screenshots of a working SWAT stuffer’s user panel, and those images show that SWAT currently lists more than 1,200 drops in the United States that are available for stuffers to rent. The contact information for Kareem, a young man from Maryland, was listed as an active drop. Contacted by KrebsOnSecurity, Kareem agreed to speak on condition that his full name not be used in this story.
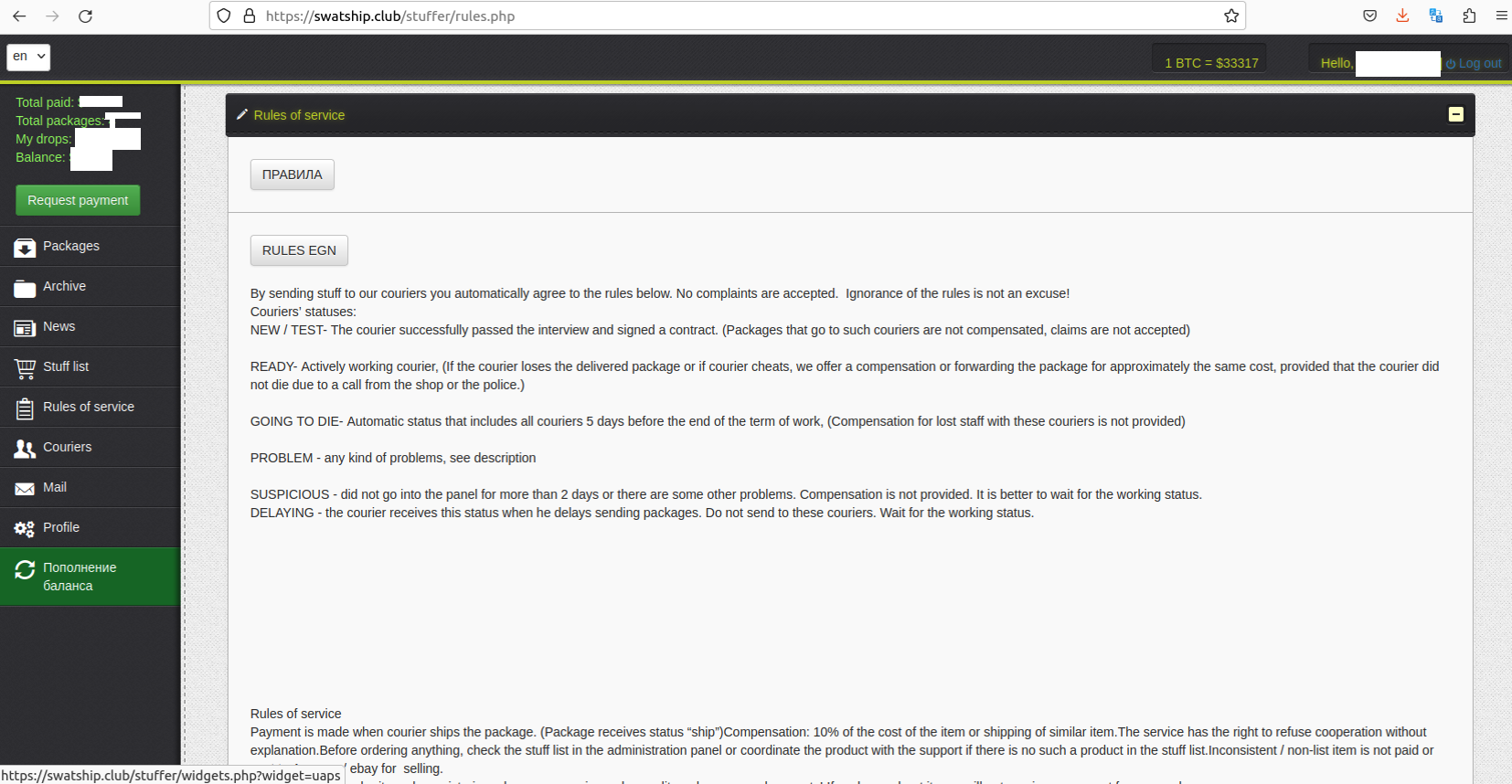
A SWAT panel for stuffers/customers. This page lists the rules of the service, which do not reimburse stuffers for “acts of god,” i.e. authorities seizing stolen goods or arresting the drop.
Kareem said he’d been hired via an online job board to reship packages on behalf of a company calling itself CTSI, and that he’s been receiving and reshipping iPads and Apple watches for several weeks now. Kareem was less than thrilled to learn he would probably not be getting his salary on the promised payday, which was coming up in a few days.
Kareem said he was instructed to create an account at a website called portal-ctsi[.]com, where each day he was expected to log in and check for new messages about pending shipments. Anyone can sign up at this website as a potential reshipping mule, although doing so requires applicants to share a great deal of personal and financial information, as well as copies of an ID or passport matching the supplied name.

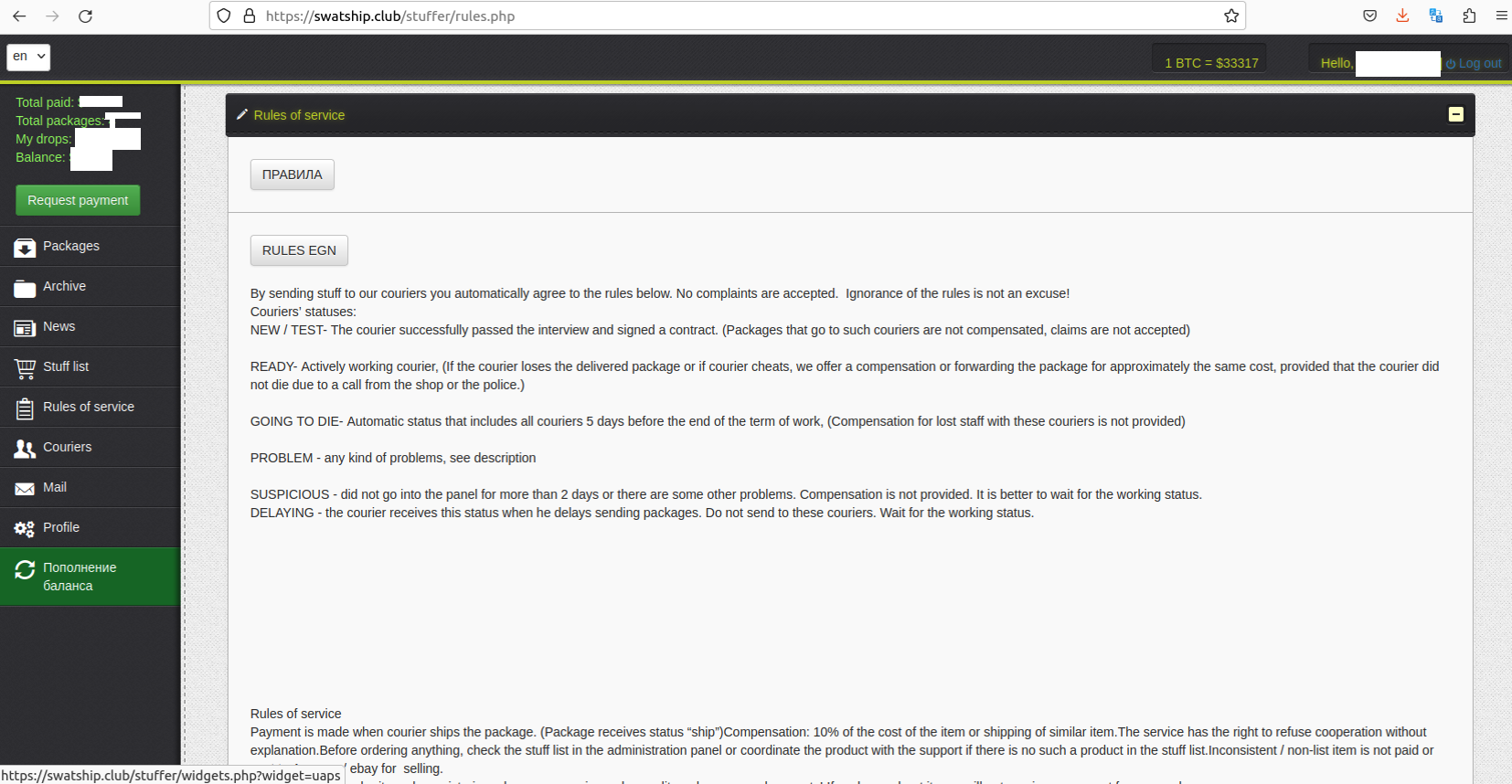
A SWAT panel for stuffers/customers, listing hundreds of drops in the United States by their status. “Going to die” are those who are about to be let go without promised payment, or who have quit on their own.
On a suspicion that the login page for portal-ctsi[.]com might be a custom coding job, KrebsOnSecurity selected “view source” from the homepage to expose the site’s HTML code. Grabbing a snippet of that code (e.g., “smarty/default/jui/js/jquery-ui-1.9.2.min.js”) and searching on it at publicwww.com reveals more than four dozen other websites running the same login panel. And all of those appear to be geared toward either stuffers or drops.
In fact, more than half of the domains that use this same login panel actually include the word “stuffer” in the login URL, according to publicwww. Each of the domains below that end in “/user/login.php” are sites for active and prospective drops, and each corresponds to a unique fake company that is responsible for managing its own stable of drops:
lvlup-store[.]com/stuffer/login.php
personalsp[.]com/user/login.php
destaf[.]com/stuffer/login.php
jaderaplus[.]com/stuffer/login.php
33cow[.]com/stuffer/login.php
panelka[.]net/stuffer/login.php
aaservice[.]net/stuffer/login.php
re-shipping[.]ru/stuffer/login.php
bashar[.]cc/stuffer/login.php
marketingyoursmall[.]biz/stuffer/login.php
hovard[.]xyz/stuffer/login.php
pullback[.]xyz/stuffer/login.php
telollevoexpress[.]com/stuffer/login.php
postme[.]today/stuffer/login.php
wint-job[.]com/stuffer/login.php
squadup[.]club/stuffer/login.php
mmmpack[.]pro/stuffer/login.php
yoursmartpanel[.]com/user/login.php
opt257[.]org/user/login.php
touchpad[.]online/stuffer/login.php
peresyloff[.]top/stuffer/login.php
ruzke[.]vodka/stuffer/login.php
staf-manager[.]net/stuffer/login.php
data-job[.]club/stuffer/login.php
logistics-services[.]org/user/login.php
swatship[.]club/stuffer/login.php
logistikmanager[.]online/user/login.php
endorphine[.]world/stuffer/login.php
burbon[.]club/stuffer/login.php
bigdropproject[.]com/stuffer/login.php
jobspaket[.]net/user/login.php
yourcontrolboard[.]com/stuffer/login.php
packmania[.]online/stuffer/login.php
shopping-bro[.]com/stuffer/login.php
dash-redtag[.]com/user/login.php
mnger[.]net/stuffer/login.php
begg[.]work/stuffer/login.php
dashboard-lime[.]com/user/login.php
control-logistic[.]xyz/user/login.php
povetru[.]biz/stuffer/login.php
dash-nitrologistics[.]com/user/login.php
cbpanel[.]top/stuffer/login.php
hrparidise[.]pro/stuffer/login.php
d-cctv[.]top/user/login.php
versandproject[.]com/user/login.php
packitdash[.]com/user/login.php
avissanti-dash[.]com/user/login.php
e-host[.]life/user/login.php
pacmania[.]club/stuffer/login.php
Why so many websites? In practice, all drops are cut loose within approximately 30 days of their first shipment — just before the promised paycheck is due. Because of this constant churn, each stuff shop operator must be constantly recruiting new drops. Also, with this distributed setup, even if one reshipping operation gets shut down (or exposed online), the rest can keep on pumping out dozens of packages a day.
A 2015 academic study (PDF) on criminal reshipping services found the average financial hit from a reshipping scheme per cardholder was $1,156.93. That study looked into the financial operations of several reshipping schemes, and estimated that approximately 1.6 million credit and debit cards are used to commit at least $1.8 billion in reshipping fraud each year.
It’s not hard to see how reshipping can be a profitable enterprise for card crooks. For example, a stuffer buys a stolen payment card off the black market for $10, and uses that card to purchase more than $1,100 worth of goods. After the reshipping service takes its cut (~$550), and the stuffer pays for his reshipping label (~$100), the stuffer receives the stolen goods and sells them on the black market in Russia for $1,400. He has just turned a $10 investment into more than $700. Rinse, wash, and repeat.
The breach at SWAT exposed not only the nicknames and contact information for all of its stuffers and drops, but also the group’s monthly earnings and payouts. SWAT apparently kept its books in a publicly accessible Google Sheets document, and that document reveals Fearlless and his business partner each routinely made more than $100,000 every month operating their various reshipping businesses.
The exposed SWAT financial records show this crime group has tens of thousands of dollars worth of expenses each month, including payments for the following recurring costs:
-advertising the service on crime forums and via spam;
-people hired to re-route packages, usually by voice over the phone;
-third-party services that sell hacked/stolen USPS/Fedex labels;
-“drops test” services, contractors who will test the honesty of drops by sending them fake jewelry;
-“documents,” e.g. sending drops to physically pick up legal documents for new phony front companies.
The spreadsheet also included the cryptocurrency account numbers that were to be credited each month with SWAT’s earnings. Unsurprisingly, a review of the blockchain activity tied to the bitcoin addresses listed in that document shows that many of them have a deep association with cybercrime, including ransomware activity and transactions at darknet sites that peddle stolen credit cards and residential proxy services.
The information leaked from SWAT also has exposed the real-life identity and financial dealings of its principal owner — Fearlless, a.k.a. “SwatVerified.” We’ll hear more about Fearlless in Part II of this story. Stay tuned.
https://krebsonsecurity.com/2023/11/russian-reshipping-service-swat-usa-drop-exposed/